Internet Control Message Protocol
Here comes another article I wrote for the “Communication Networks I” bonus system:
Internet Control Message Protocol
The Internet Control Message Protocol (ICMP) is used to communicate error and management messages between IP peers. ICMP data is transported in IP packages (protocol = 1), but because it is an integral part of IP, it is classified as a member of layer 3.
Structure of an ICMP packet
Each ICMP message is categorized by a type and a code (-> links section). In addition, a 16 bit checksum is calculated and stored in the header.
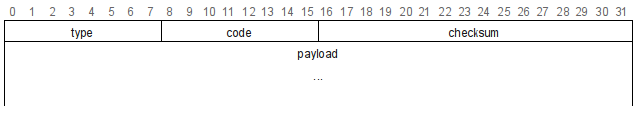
Structure of an ICMP header
The rest of an ICMP packet (payload) depends on the type of message.
Message types
RFC 1122 divides the ICMP messages into error and query messages:
Error messages
Error messages are used to communicate problems that occurred while transmitting an IP packet. They usually include the IP header and at least the first 8 bytes of the packet that caused the error.
Error messages must NOT be sent as a reply to other ICMP error messages, fragments (exception: first fragment) and packets with source and/or destination addresses that describe no single host (broadcast, multicast, loopback, …). This is neccessary to prevent a situation where ICMP traffic uses much of the available bandwidth, also known as a packet storm.
Destination Unreachable
If an IP packet could not be delivered to it’s destination, a “Destination Unreachable” message is sent to the sender. It carries a status code that describes the problem. Some examples for this code are net/host/protocol/port unreachable, host/network unknown or fragmentation needed but “Don’t Fragment” bit set.
Redirect
A redirect is sent by a gateway if it is in the same subnet as the sender of the packet and it received the packet through another gateway. The redirect message tells the sender to send new packets for the destination host or network directly using this gateway.
Source Quench
It may occur that some gateways or the destination host of a packet receive packets faster than they can process them. If this happens, packets are discarded if no counter measures are taken. If the receiving buffer of a gateway or host is about to reach its limits, it is allowed for this station to send a source quench message to the sender. A station that receives a source quench should lower the data rate at which it is sending to the current receiver.
Time Exceeded
There are two types of time exceeded messages:
- If a gateway receives a packet with the TTL field set to 1, it needs to discard it because it timed out.
- If a target host does not receive all fragments of a packet before its TTL is reached, this packet is discarded.
In both cases, the station discarding the message may send a time exceeded notification to the sender. Please note that it is not required to do so!
Parameter Problem
This message is usually sent if the header of a packet contains errors. It often indicates an error in the sending host’s IP implementation. It is also used as a catch-all error message that is sent when no other message fits in and the packet could not be processed.
Query messages
Query messages are used to get information about another station in the network or for testing purposes. The receiver of a query packet should send a response with the requested information.
Echo
If a host receives an echo message, it sends back an echo reply message, including the unmodified data that was sent as a payload with the echo request. This is used to check whether a specific host can be reached and how much time a packet needs to travel to the receiver and back again (roundtrip time). On most operating systems, echo messages can be sent using the command “ping”. An example invocation may look like this:
$ ping www.tu-darmstadt.de
PING www-tu.hrz.tu-darmstadt.de (130.83.47.128) 56(84) bytes of data.
64 bytes from www-tu.hrz.tu-darmstadt.de (130.83.47.128): icmp_seq=1 ttl=52 time=15.0 ms
64 bytes from www-tu.hrz.tu-darmstadt.de (130.83.47.128): icmp_seq=2 ttl=52 time=12.0 ms
64 bytes from www-tu.hrz.tu-darmstadt.de (130.83.47.128): icmp_seq=3 ttl=52 time=13.8 ms
--- www-tu.hrz.tu-darmstadt.de ping statistics ---
3 packets transmitted, 3 received, 0% packet loss, time 2000ms
rtt min/avg/max/mdev = 12.096/13.662/15.033/1.214 ms
Information
Deprecated: This was used by hosts to query their network address. Nowadays, this is done using alternative protocols such as DHCP.
Timestamp
Timestamp messages can be used to synchronize the clocks of hosts in the network. The sender puts its timestamp (“originate timestamp”) in the packet when it leaves the host. The receiver appends the time the packet is received (“receive timestamp”) and the time the reply is sent (“transmit timestamp”) and sends it back to the originator. The timestamp is defined as the number of milliseconds since midnight, UTC.
Address Mask
Address masks - also known as subnet masks - are used to specify the range of IP addresses belonging to a specific subnet. When a host sends an address mask query, it should receive an answer, containing the correct mask for the current subnet.
Conclusion
This article is limited to the message types discussed in RFC 1122, which were defined in RFCs 792 and 950. In the meantime, some extensions such as RFC 1256 (router discovery) were created. The complete list of types registered with the Internet Assigned Numbers Authority (IANA) can be found in the links section.
Links
- RFC 792 (ICMP)
- RFC 950, Appendix I (defines the address mask message)
- RFC 1122, Section 3.2.2
- IANA: ICMP type numbers reference